The Lurker
Staggering ignorance, or how to convince people you don't know anything about computer security
Victoria puts blind faith in electronic voting:
"The system is standalone, it's not like in the US where it is networked, so it can't be hacked," says Sue Lang, VEC communications manager.
Lang's statement betrays a profound ignorance about computer security. A network connection has absolutely no bearing on whether or not an electronic voting machine is vulnerable to tampering. Physical access to the hardware (which is obviously necessary in a voting appliance) presents huge risks.
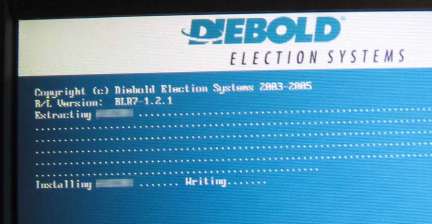
I haven't yet seen Hacking Democracy, the documentary referred to in the article from The Age. The photograph above comes from Critical Security Issues with Diebold TSx (PDF), a report written by Harri Hursti, who contributed to the documentary. Hursti discovered that this model of voting machine will automatically install software if a PCMCIA card is inserted when the machine boots. Because this voting machine is a general-purpose computer running Windows PC, that alone means that anyone with sufficient knowledge can make the voting machine do anything they want — whether that be to create a false total of votes, misrepresent the candidates' party allegiances, or to inconvenience voters by rendering the voting machine(s) inoperable. And this is only one of the machine's several catastrophic design errors.
A completely unrelated voting machine is being used in the coming Victorian election, and the Victorian Electoral Commission claims that Extensive tests conducted by the VEC and an independent expert auditor who will also examine the source code to ensure that voting is secure, accurate and free from any malicious code
, but there's no sign of any published report from the auditor on the VEC's web site, so there is no way to know how thorough and effective the audit was.
I have to hope that the HP/Scytl voting machine is more secure than Diebold's product, but the only justification I have for that hope is that I can't imagine how it could be worse.
Related topics: Politics Mindless Link Propagation
All timestamps are Melbourne time.